In this post we will learn how to set up multi-organization tenancy for vRealize Automation 8.1using Lifecycle ManagervRealize Suite Lifecycle Manager.
Enabling tenancy creates a new Provider organization. The Provider Admin can create new tenants, add tenant admins, setup directory synchronization, and add users. Tenant admins can also control directory synchronization for their tenant and will grant users access to services within their tenant. Additionally, tenant admins will configure Policies, Governance, Cloud Zones, Profiles, access to content and provisioned resources; within their tenant. A single shared SDDC or separate SDDCs can be used among tenants depending on available resources. In addition to their other privileges, Provider Admins can also act as Tenant Admins.
Before enabling tenancy, there are a number of prerequisites.
Prerequisites
Install and configure Workspace ONE Accessversion 3.3.2.
Install and configure vRealize Suite Lifecycle Manager version 8.1
Procedure:
1- Create the required A and CNAME Type DNS records.
For single node deployments, the vRealize Automation FQDN points to the vRealize Automation appliance, and the Workspace ONE Access FQDN points to the Workspace ONE Access appliance.
For cluster deployments, both the Workspace ONE Access and vRealize Automation tenant-based FQDNs must point to their respective load balancers. Workspace ONE Access is configured with SSL Termination, so the certificate is applied on both the Workspace ONE Access cluster and load balancer. The vRealize Automation load balancer uses SSL passthrough, so the certificate is applied only on the vRealize Automation cluster.
2- Create or import the required multi-domain (SAN) certificates for both Workspace One 3.3.2 and vRA 8.1
You can create certificates in Lifecycle Manager using the Locker service that enables you to create certificates licenses, and passwords. Alternatively, you can use a CA server or some other mechanism to generate certificates.
If you need to add or create additional tenants, you must recreate and apply your vRealize Automation and Workspace ONE Access tenants.
After you create your certificates, you can apply then with in Lifecycle Manager using the Lifecycle Operations feature.
You must select the environment and product and then the Replace Certificate option on the righthand menu.
Then you can select the product. When you replace a certificate, you must re-trust all associated products in your environment.
You must wait for the certificate to be applied and all services to restart before proceeding to the next step. (VIDM)
3- Apply the Workspace One SAN certificate on the Workspace ONE Access instance or cluster.
4- In vRealize Suite Lifecycle Manager 8.1, run the Enable Tenancy wizard to enable mult-tenancy and create an alias for the default master tenant.
5- Enabling tenancy requires that you create an alias for the provider organization master tenant or default tenant. After you enable tenancy, you can access Workspace ONE Access via the master tenant FQDN.
6- Apply the vRA SAN certificates on the vRealize Automation instance or cluster.
You can apply SAN certificates through the Lifecycle Manager Lifecycle Operations service. You need to view the details of the environment and then select Replace Certificates on the right menu. You must wait for the certificate replacement task to complete before adding tenants. As part of certificate replacement, vRealize Automation services will restart.
7- In Lifecycle Manager, run the Add Tenants wizard to configure the desired tenants.
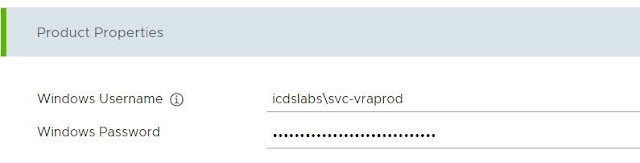
You add tenants using the Lifecycle Manager Tenant Management page located under Identity and Tenant Management. You can only add tenants for which you have previously configured certificates and DNS settings.
When creating a tenant, you must designate a tenant administrator
you can select the Active Directory connections for this tenant.
You must also select product or product instance to which the tenant will be associated.
You need to run precheck validation to validate prerequisite.
Note - If you do not meet prerequisite then you will get error during precheck task . In my case DNS entry mapping was missing for VIDM and vRA.
Once Validation done then you need to click on create tenant
Now Time to monitor requests to get create new tenant for us.
Tenant is created successfully and ready for test first time in vRA8.1
we are able to login on newly created Tenant with Tenant administrator ID :)
I hope you enjoy reading this blog as much as I enjoyed writing it. Feel free to share this on social media if it is worth sharing.